This is an extended newsletter, so it may be truncated towards the end of the email. To read the full post, just select the View entire message hyperlink at the bottom of the email or Open in Browser!
Breaking Bank - Ursnif moves to enabling ransomware
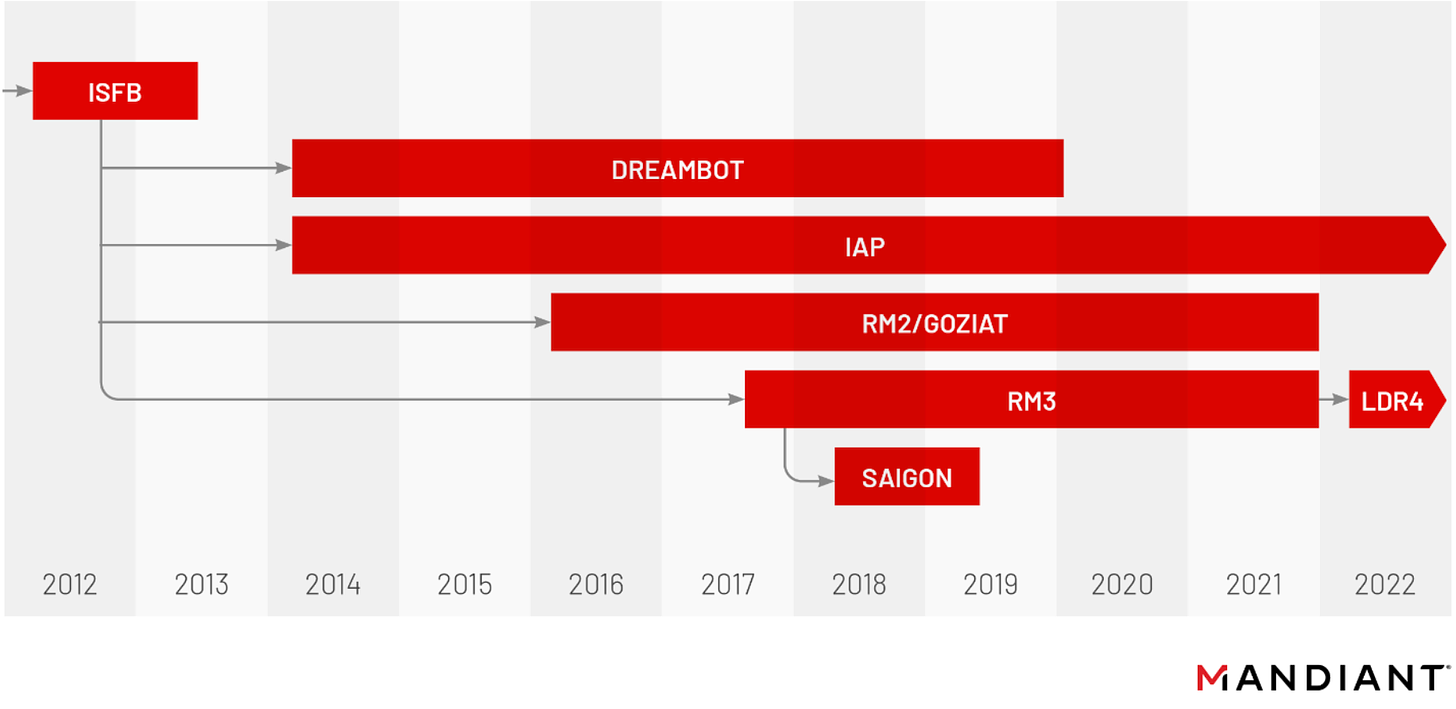
Mandiant have reported that Ursnif (a.k.a. Gozi, Gozi/IFSB), a banking trojan with lineage dating back to 2012, has abandoned its roots - opting instead to join in the ransomware rat race as an all-purpose backdoor.
The LDR4 variant of the Ursnif loader is an evolution of what Mandiant note is “the most sophisticated version to date” - the RM3 build - which has been distributed primarily in Oceania and the UK since emerging in 2017. Both variants were observed being delivered via malicious Office documents and hijacked email threads.
While it’s still early days, given they are believed to be distributed by the same actor - UNC2420 - it is possible their distribution methods and targeting will remain relevant.
In a detailed analysis of the new variant’s code, Mandiant note its banking-related capabilities have been completely removed, in addition to the implementation of a “mix of code refactoring, regressions and interesting simplification strategies.”
Ursnif joins IcedID & Qakbot on the watchlist of first-stage malware that may lead to ransomware, though it remains to be seen how prolific they will be and who they partner with.
Mandiant have included various detection strategies and a YARA rule in their report that will help you get started in mounting your defence, while @Kostastsale has provided an excellent summary of Ursnif’s key IoAs and characteristics to look out for:


Text4Shell - more of a molehill than mountain
Twitter has helpfully assigned CVE-2022-42889 - a code execution vulnerability in Apache Commons Text Library versions 1.5 - 1.9 - a “_____4Shell” moniker, triggering the PTSD baked-into CISOs around the world from the Log4Shell vulnerability of last year.
Dubbed “Text4Shell”, it’s actually more similar to the Spring4Shell vulnerability, which was only exploitable in specific implementations.
Text4Shell requires the StringSubstitutor.createInterpolator() method to accept remote user input, which can be abused to run commands via the JVM script execution engine; perform specific DNS lookups, or connect to specified URLs.
While Maven Repository noted as many as 2,593 projects use the vulnerable library, Threat Intel vendor Flashpoint has poured cold water on that stat by pointing out that very few of those listed use the vulnerable method.
PoC exploit code has been shared widely through Github, with attempts to exploit the vulnerability being observed from the 18th of October.
The bottom line: In spite of the eye-catching CVSS 9.8 score this vulnerability was assigned, the actual potential for exploitation is much more limited. Version 1.10 of the library fixes the underlying vulnerability, so patching is also a cinch.
Topical as ever, Checkpoint researchers have shared this detailed technical overview of the BlackBasta ransomware operation and encryptor;
The BlackByte ransomware group have been observed employing a new data stealing tool called ExByte. Written in Go, it comes with inbuilt anti-analysis checks and pushes stolen files to the Mega cloud storage service;
Microsoft have written up a DART response to a Cuba Ransomware infection, breaking down the infection chain, TTPs used, and several ways to detect these activities;
Trend Micro have expanded on previous speculation by AquaSec that TeamTNT had returned, suggesting it was in fact another crypto-mining group called WatchDog;
The Deadbolt ransomware group - having been swindled of 150 decryption keys by Dutch cyber police last week - have been observed attempting to extort NAS manufacturer QNAP, asking 10 BTC for technical details of an 0-day they abused or 50 BTC to provide the master decryption key for all victims of their campaign.
Qakbot stomps payload post-injection, HTML Smuggling detection still a weakness for AV
@Kostastsale noticed a sample distributed by the Obama botnet early in the week overwriting its payload dll once injected into process memory, in an apparent attempt to “prevent analysis and possible retroactive static detection.”
While this initially appeared to be a newly adopted tactic, it was pointed out that this actually is an old TTP that has re-emerged in this campaign.
That old Qakbot TTPs can become relevant again if it suits them is in itself worth noting. Given recent changes to their payload obfuscation and implementation of persistence mechanisms, Qakbot developers appear to be actively working to reduce the detect-ability of their campaigns.
This appears to be paying dividends in their use of HTML Smuggling, with one sample going undetected by 61 Antivirus engines - a figure that only improved to 12/60, six days later.
Bumblebee goes old school
A campaign this week observed by @ExecuteMalware shows the actor has gone back to the classics in order to mix up their payload delivery mechanisms, swapping out the ZIP > VHD/ISO > LNK > DLL delivery chain for social engineering to deliver an Excel maldoc.
The delivery chain began with the actor initiating contact through a web form, before engaging in subsequent email exchanges to add legitimacy to their conversation.
The final step was to deliver a macro-enabled Excel document that masqueraded as a DocuSign-encrypted proposal document. This dropped and ran the final payload with regsvr32.exe, completing the delivery chain.
If this all sounds very familiar, it’s because this same method was used as recently as March this year to deliver BazarBackdoor payloads - the predecessor to the Bumblebee Loader that EXOTICLILY now sling on behalf of former Conti ransomware affiliates.
Given this, it’s worth considering what other TTPs associated with BazarLoader/BazarBackdoor campaigns may resurface. Those old write-ups and detection rules may still have some life in them yet!
Innovative Bad Guy: Moar passwords moar better
Trustwave researchers have highlighted the recent uptick in the use of password-protected archives by malware distributors, pointing to a campaign where the end payload attempted to evade automated inspection by hiding behind up to four layers of containers/archives.
It’s onion-esque nature aside, this campaign is noteworthy for its use of self-extracting (SFX) archives.
This file format is valuable for its ability to stymie static analysis measures by implementing password-protection, while crucially not requiring the user to manually enter a password to extract and run the final payload.
On the whole, the use of password-protected archives - of which 96% of observed instances were attributed to Emotet by Trustwave - is one to keep across and on the lookout for.
Microsoft No-Fix in Office Online Server
Manish Tanwar of MDSec has uncovered a SSRF vulnerability in Office Online Server, a product provides users the ability to view and edit corporate Office documents from within their browser. This vulnerability not only enables enumeration of internal resources but - under the right conditions - can allow the attacker to achieve code execution on the server itself.
Simply providing a HTTP or UNC location to the /op/view.aspx endpoint (retrieves remote resources to display within the browser) is enough to enable a timing attack that allows an attacker to infer valid internal IP addresses.
Better yet, if the Server can communicate with an attacker-controlled SMB server, the same request can be used to coerce and relay authentication to ADCS. Because the Server runs using the machine account, ADCS will provide a TGT for said account that can be used to achieve local admin privileges on the Server itself.
Volume-based alerting might help surface attempts to abuse this to enumerate internal resources, while existing methods used to identify NTLM relay attempts will flag anyone trying to elevate privileges using this technique.
As mentioned, this is another Microsoft no-fix special, so it’s open to abuse in perpetuity.
Azure Service Fabric Explorer (SFXv1) enables hijacking of Azure Service Fabric clusters
Microsoft have addressed a spoofing vulnerability in the management App for Azure Service Fabric clusters - Service Fabric Explorer (CVE-2022-35829).
Identified by Orca Security, the vulnerability allowed “Deployer” users to “create a malicious application name and abuse the Administrator permissions to perform various calls and actions” - ultimately enabling a full takeover of Azure Service Fabric clusters.
Service Fabric is a platform for hosting business-critical applications, including numerous Microsoft products such as Microsoft Intune, Cortana, Power BI, and more.
There have been no instances of exploitation of this vulnerability in-the-wild.
Note that this has been fixed in the current default SFX web client - SFXv2 - and users are urged to upgrade to this version to avoid the vulnerability.
While it’s still possible to manually deploy the older, vulnerable client (SFXv1) - Microsoft are asking nicely that you don’t, and promise they’ll remove that option in a future release.
Offensive
Regulator - A tool that uses first-round scanning results and permutation-guessing to identify additional subdomains based on naming convention;
WAMBam - The result of Adam Chester’s weekend (yes, just the weekend) exploring how Azure auth tokens are stored and loaded into Microsoft Office. This write-up expands on that, as well as how to recover them from the Token Broker cache, and Microsoft Account tokens (different from Azure AD) through poking the wlidsvc Service via RPC;
CrackMapExec has gotten a new module to dump Microsoft Teams cookies, which can be used to enumerate user information and messages;
Cube0x0 is back with part 2 in their series on relaying YubiKeys - this time relaying authentication challenges and responses between a protected service and connected FIDO2 Yubikey;
Make like Smaug and add this to your collection, even if you don’t need it - another exhaustive cheatsheet on Active Directory enumeration.
Defensive
Antignis - a tool to help configure the host-based firewall on Windows workstations and servers that are part of an AD Domain;
Typosquatting-finder - As it says on the can - a tool that identifies and lists potentially typo-squatted domains;
DocIntel - a self-hosted tool to help centralise and sort your threat intelligence. Great for orgs that don’t want to jump into the Atlassian stack or are short on budget;
osquery-defense-kit - a collection of >130 “production-ready” (maybe try it in test first anyway) OSQuery queries aimed at assisting malware alerting and investigation efforts;
CISA have released SCuBA - a series of security configuration baselines for Microsoft 365, and ScubaGear - a tool to help assess your tenant against it. While it might not be mandatory for your organisation, this is one to bookmark if for nothing else than a guidepost to help configure your own baseline;
Not something new, but definitely something useful - an index of public reporting on APT-grade threat groups;
Expand your telemetry by configuring an Elastic ingest pipeline for Sysmon for Linux;
Red Canary have shared a great wrap-up of the types of worms, some behaviours exhibited by various worms throughout history, and how they might be detected;
CyberArk have published Part 1 of a series looking into Rootkits, with this issue providing a detailed summary of how they work and many ways they can be implemented;
Azure AD Principals and Access Permissions are a tumbleweed of conflicting naming conventions and abstract linkages - this blog attempts to decipher it, and may be helpful for those looking to understand it better.
Microsoft suffered a nightmare leak of sensitive information for over 65,000 customer organisations - all from an unsecured Azure storage blob. The whole saga was poorly handled by both SOCRadar who disclosed the leak, and Microsoft who begrudgingly owned up to it while simultaneously panning SOCRadar’s actions. Quite the drama - check out this thread for a neat chronological wrap-up;
Presentations for the 10th EU ATT&CK Community Workshop are available here;
KC7 - a cyber security game built for Azure Data Explorer;
Kusto Detective Agency - a game that will help practice your KQL skills.